possibility of inheriting multiple resource group tags to underlying resources #40
-
|
Great work here. Just seeking the possibility of adding multiple tags here. Some kind of guidance would be awesome. Thanks module "team_a_mg_inherit_resource_group_tags_modify" {
source = "gettek/policy-as-code/azurerm//modules/def_assignment"
version = "2.6.1"
definition = module.inherit_resource_group_tags_modify.definition
assignment_scope = data.azurerm_management_group.team_a.id
assignment_effect = "Modify"
skip_remediation = null
remediation_scope = data.azurerm_subscription.current.id # change the scope of remediation tasks, defaults to assignment_scope
assignment_parameters = {
tagName = "environment"
}
} |
Beta Was this translation helpful? Give feedback.
Replies: 1 comment 1 reply
-
|
Hi @chanakanissanka. Managing multiple tags with built-in or custom Policies is unfortunately a little tricky so understand the frustration. One way I've overcome this is by creating multiple custom definitions for each Tag using the native resource See also: #37 locals {
tag_names = [
"Application Name",
"Cost Center",
"Environment",
]
}
resource "azurerm_policy_definition" "modify_sub_inherit_tags" {
for_each = toset(local.tag_names)
name = "modify_inherit_sub_tag_${lower(replace(each.value, " ", "_"))}"
display_name = "Inherit ${each.value} tag from the subscription"
description = "Adds or replaces ${each.value} tag and value from the containing subscription when any resource is created or updated. Existing resources can be remediated by triggering a remediation task."
policy_type = "Custom"
mode = "Indexed"
management_group_id = data.azurerm_management_group.org.id
metadata = jsonencode(
{
"category" : "Tags",
"version" : "1.0.0"
}
)
parameters = jsonencode(
{
"effect" : {
"type" : "String",
"defaultValue" : "Modify",
"allowedValues" : [
"Modify",
"Disabled"
],
"metadata" : {
"displayName" : "Effect",
"description" : "The effect determines what happens when the policy rule is evaluated to match"
}
},
"excludedResourceTypes" : {
"type" : "Array",
"metadata" : {
"displayName" : "Excluded Resource Types",
"description" : "List of resource types to exclude",
"strongType" : "resourceTypes"
},
"defaultValue" : [
"microsoft.resources/subscriptions"
]
}
}
)
policy_rule = jsonencode(
{
"if" : {
"allOf" : [
{
"field" : "type",
"notIn" : "[parameters('excludedResourceTypes')]"
},
{
"allOf" : [
{
"field" : "[concat('tags[', '${each.value}', ']')]",
"notEquals" : "[subscription().tags['${each.value}']]"
},
{
"value" : "[subscription().tags['${each.value}']]",
"notEquals" : ""
}
]
}
]
},
"then" : {
"effect" : "[parameters('effect')]",
"details" : {
"roleDefinitionIds" : [
"/providers/microsoft.authorization/roleDefinitions/4a9ae827-6dc8-4573-8ac7-8239d42aa03f"
],
"operations" : [
{
"operation" : "addOrReplace",
"field" : "[concat('tags[', '${each.value}', ']')]",
"value" : "[subscription().tags['${each.value}']]"
}
]
}
}
}
)
lifecycle {
create_before_destroy = true
}
timeouts {
read = "10m"
}
}
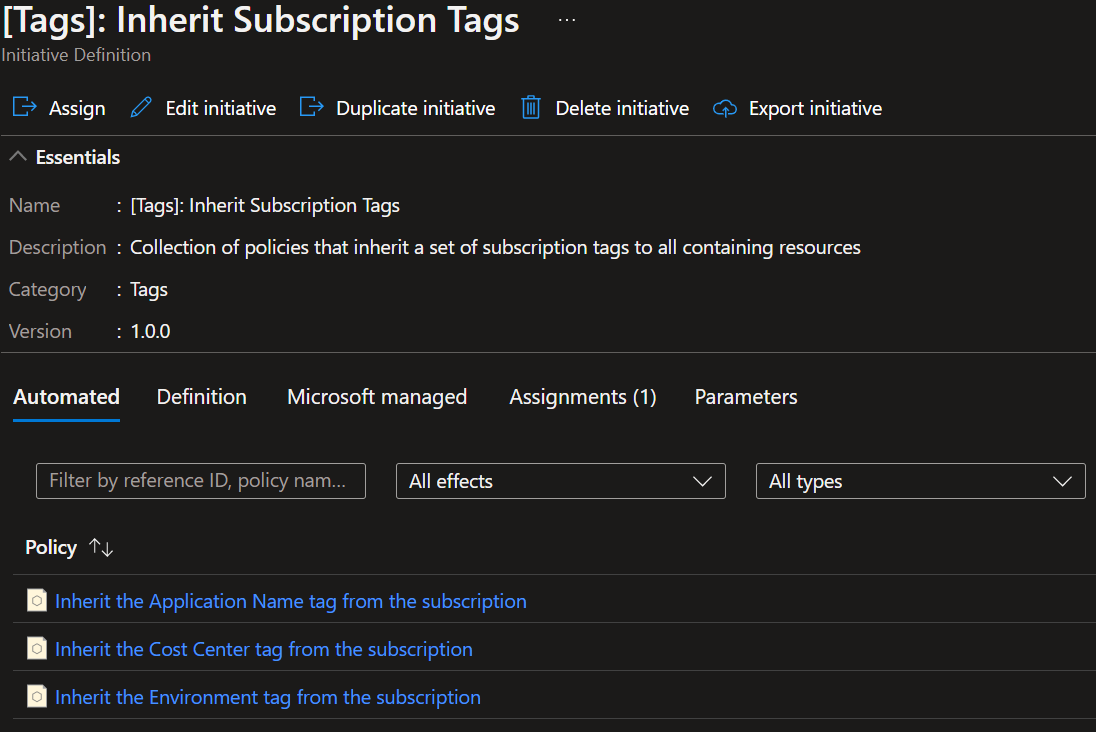
module "inherit_subscription_tags" {
source = "..//modules/initiative"
initiative_name = "inherit_subscription_tags"
initiative_display_name = "[Tags]: Inherit Subscription Tags"
initiative_description = "Collection of policies that inherit a set of subscription tags to all containing resources"
initiative_category = "Tags"
merge_effects = false
management_group_id = data.azurerm_management_group.org.id
member_definitions = [
for tag in azurerm_policy_definition.modify_sub_inherit_tags :
tag
]
}
module "org_mg_inherit_subscription_tags" {
source = "..//modules/set_assignment"
initiative = module.inherit_subscription_tags.initiative
assignment_scope = data.azurerm_management_group.org.id
skip_remediation = true
skip_role_assignment = false
role_definition_ids = [
data.azurerm_role_definition.tag_contributor.id
]
assignment_parameters = {
effect_ModifyInheritSubTagApplicationName = "Modify"
effect_ModifyInheritSubTagCostCenter = "Modify"
effect_ModifyInheritSubTagEnvironment = "Modify"
}
}Hope this helps. I know it's annoying having to create multiple definitions but this will result in a somewhat dynamic way of multi-tag management that's easy to expand/contract: |
Beta Was this translation helpful? Give feedback.
Hi @chanakanissanka.
Managing multiple tags with built-in or custom Policies is unfortunately a little tricky so understand the frustration.
One way I've overcome this is by creating multiple custom definitions for each Tag using the native resource
azurerm_policy_definition, then including these in an initiative as below.See also: #37